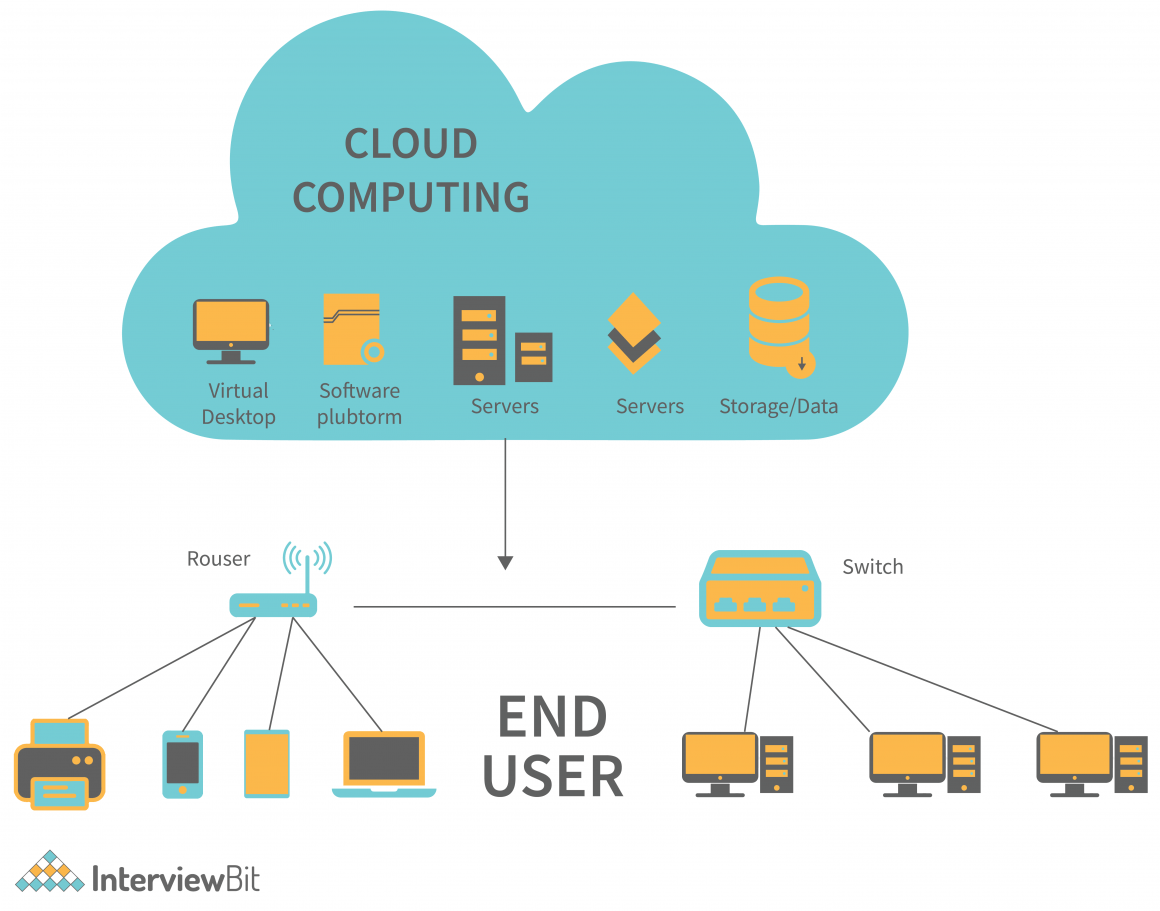
Cloud Computing everything you need to know
We will fill you in on what cloud computing is, the principles behind cloud computing and the different types of cloud computing service providers in this section. An organization’s cyber defenders should be trained on defending applications and data in the cloud and be equipped with cloud security tools. We pulled many of the lessons learned from across the department.