Cloud Computing everything you need to know
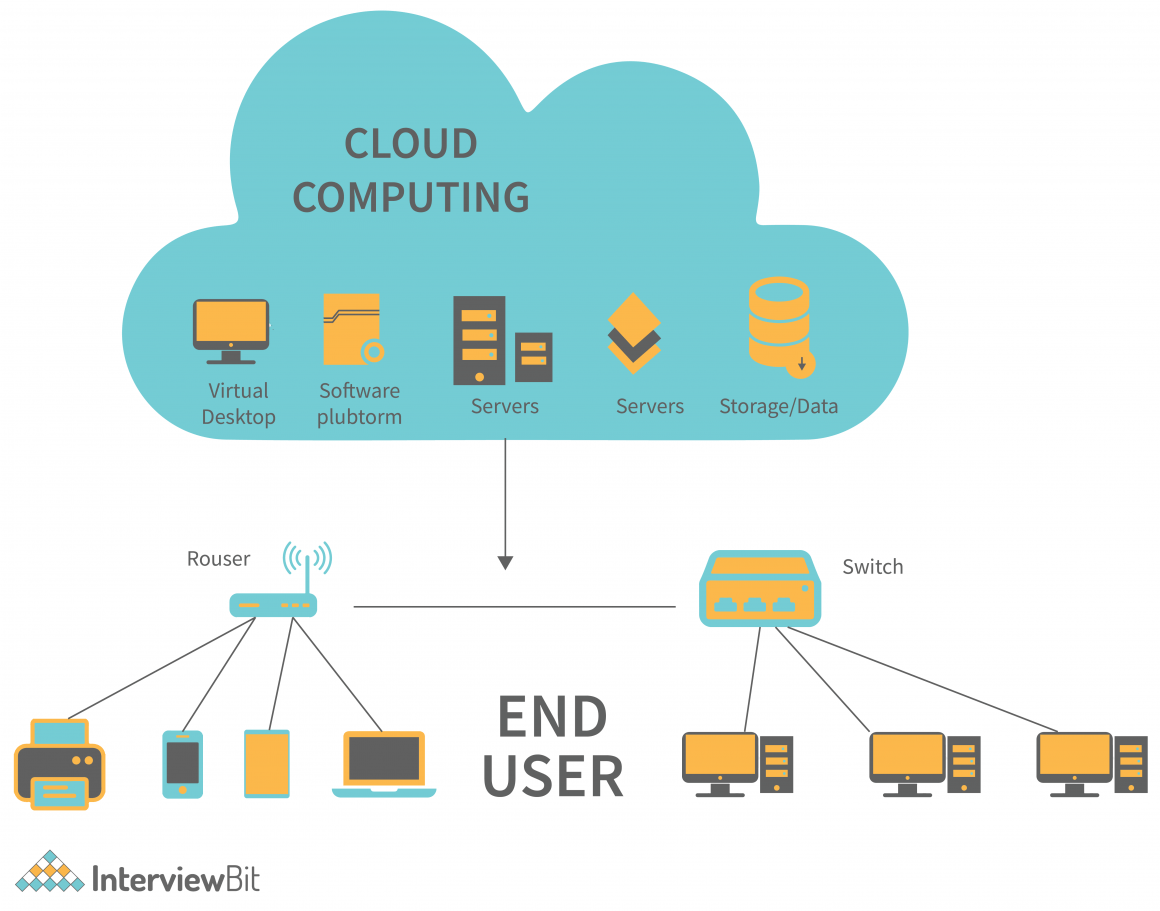
The cloud provider pools all computing resources to serve multiple customers (u.s. An organization’s cyber defenders should be trained on defending applications and data in the cloud and be equipped with cloud security tools. Actively hunt for intrusions in the cloud: There are five essential characteristics that define the cloud, as shown in the schematic below. This tool guide was.


/cdn.vox-cdn.com/uploads/chorus_image/image/63710251/20150428-cloud-computing.0.1489222360.0.jpg)