Cloud Computing Architecture Detailed Explanation InterviewBit
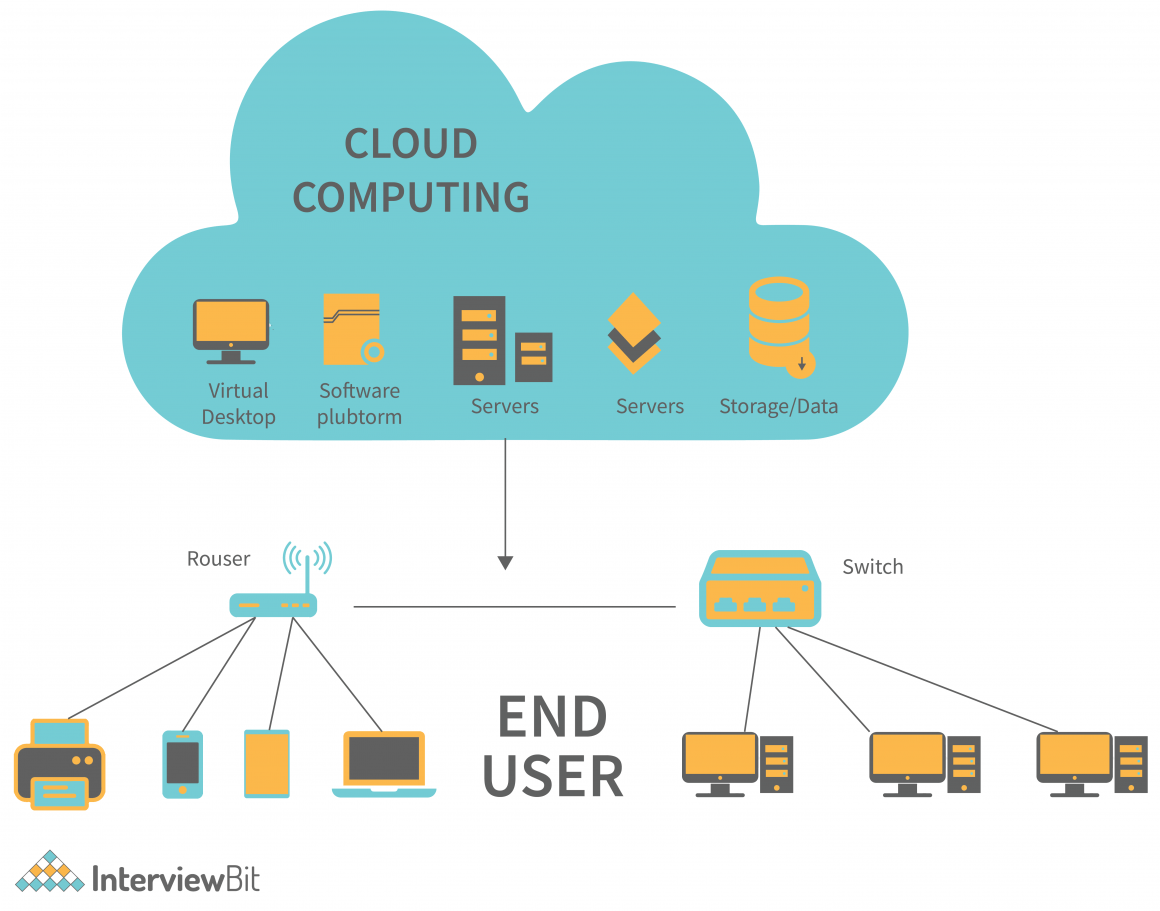
For this guide, we will not address other important and related issues like cloud. The cloud provider pools all computing resources to serve multiple customers (u.s. There are five essential characteristics that define the cloud, as shown in the schematic below. Actively hunt for intrusions in the cloud: We will fill you in on what cloud computing is, the principles.